- Industries
Industries
- Functions
Functions
- Insights
Insights
- Careers
Careers
- About Us
- Technology
- By Omega Team
Connectivity now powers nearly every aspect of life from streaming and e-commerce to smart homes, healthcare, and global finance offering immense convenience and innovation but also introducing unprecedented risks, as every device, application, and platform constantly generates vast amounts of personal and sensitive data. Protecting privacy in this interconnected ecosystem has become both a technological challenge and a moral imperative, requiring innovative solutions that can keep pace with rapidly evolving threats. Next-generation privacy technologies are emerging to meet this need, going beyond traditional firewalls and encryption by leveraging advanced cryptography, artificial intelligence, and decentralized systems to give individuals and organizations greater control over their data. These innovations not only enhance security but also build trust, enabling a digital environment where users can interact, transact, and communicate with confidence while maintaining ownership and protection of their personal information.
Why Privacy Matters More Than Ever
Privacy concerns are not new, but the scale and complexity of today’s hyperconnected world amplify them. Organizations store terabytes of customer data across cloud platforms, mobile apps, and IoT ecosystems. While this data fuels personalized experiences and smarter services, it also makes companies attractive targets for cybercriminals.
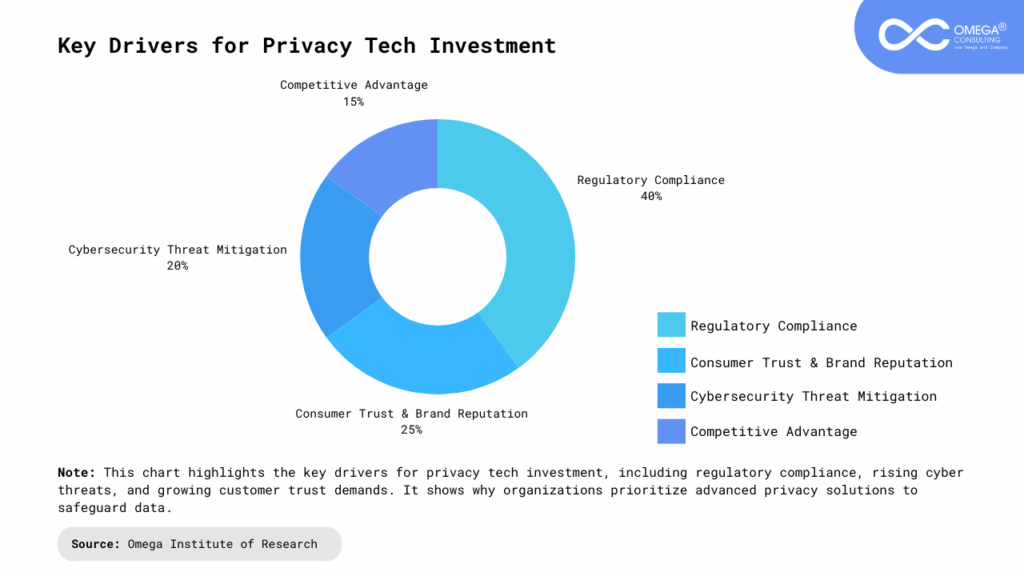
Data Breaches and Cybercrime: High-profile breaches at global companies have exposed millions of users’ records, leading to identity theft, fraud, and financial loss. These attacks are becoming more sophisticated, exploiting vulnerabilities in both technology and human behavior. Cybercriminals can monetize stolen data quickly, making prevention, monitoring, and rapid response essential components of any organization’s security framework.
Regulatory Pressure: Governments worldwide have implemented laws like the EU’s GDPR, California’s CCPA, and India’s Digital Personal Data Protection Act (DPDP). These frameworks demand greater accountability, transparency, and user consent in data handling. Non-compliance can result in hefty fines, legal actions, and reputational damage, making regulatory adherence a critical factor for global operations. Organizations must invest in robust policies, employee training, and auditing processes to ensure ongoing compliance and demonstrate their commitment to data protection.
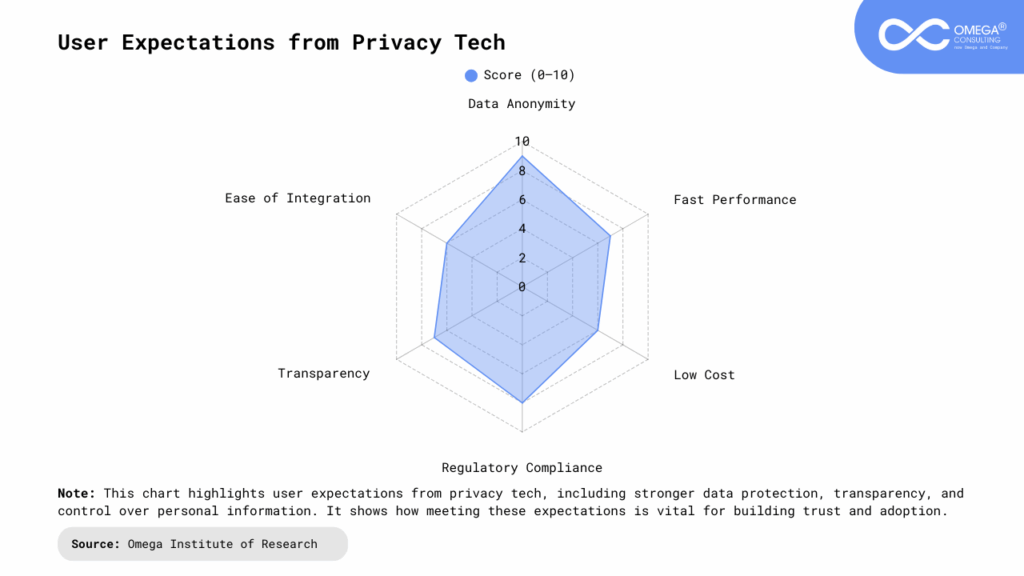
Consumer Expectations: Customers today are far more aware of privacy issues. They demand control over their data and are more likely to trust businesses that are transparent about how information is collected and used. Companies that fail to meet these expectations risk losing customers to competitors who prioritize privacy. Beyond trust, demonstrating strong privacy practices can become a key differentiator, enhancing brand loyalty, customer retention, and overall market competitiveness.
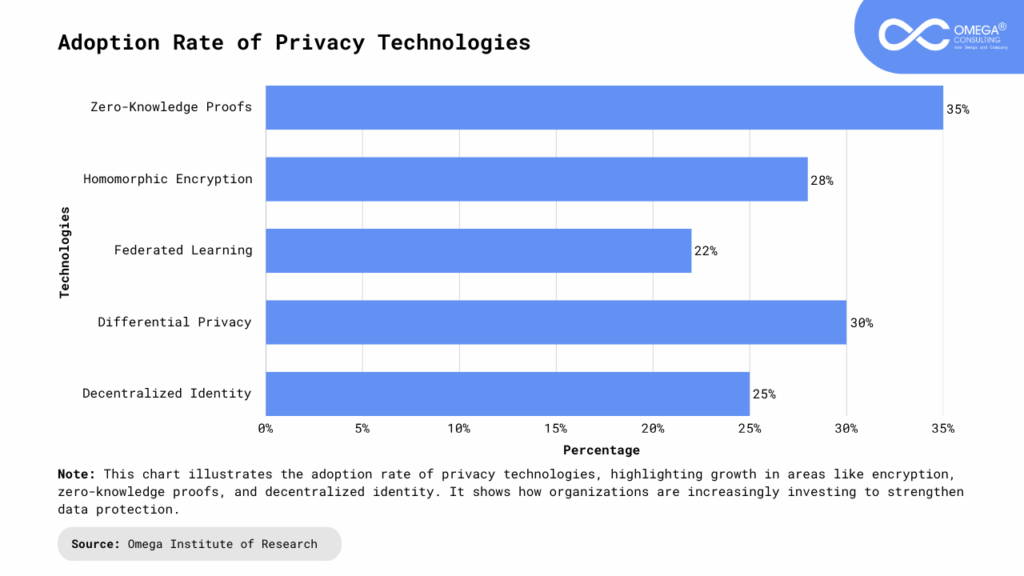
Key Next-Generation Privacy Technologies
Zero-Knowledge Proofs (ZKPs): Zero-Knowledge Proofs (ZKPs) are cryptographic techniques that allow one party to prove they know a piece of information without revealing it. The verification is done mathematically, ensuring no sensitive data is transmitted or intercepted, while confirming authenticity. ZKPs are used for digital identity verification, secure voting systems, and financial transactions. They are also applied in blockchain protocols and IoT networks to verify device authenticity without exposing underlying data. By reducing the amount of personal data shared, ZKPs limit exposure to breaches, increase trust, enable regulatory compliance, and support secure interactions even in untrusted environments.
Homomorphic Encryption: Traditional encryption methods often require decrypting data before analysis, exposing it to risk. Homomorphic encryption allows computations, such as addition, comparison, or machine learning, directly on encrypted data, with results decrypted without revealing raw information. Real-world applications include healthcare providers sharing encrypted patient data and banks running fraud detection models on encrypted financial information. Homomorphic encryption unlocks the value of sensitive datasets without risking leaks or non-compliance, supporting both security and actionable insights.
Federated Learning: Federated learning allows AI models to be trained directly on user devices, eliminating the need to centralize sensitive data. Only aggregated insights, not raw data, are shared with the central system, keeping personal information private. Google uses it for predictive text in keyboards, and voice assistants rely on it to improve speech recognition without storing conversations centrally. It is also applied in healthcare to train models on distributed data while preserving privacy. This method enables personalized services while maintaining control over sensitive information.
Differential Privacy: Differential privacy ensures individual data points cannot be traced back to specific people by adding controlled randomness to datasets, masking individual records while keeping overall patterns useful. Apple uses it to study user behavior trends, and governments employ it to publish census data safely. Differential privacy allows organizations to gain insights from large datasets without risking individual exposure, balancing analytics with confidentiality and maintaining consumer trust.
Decentralized Identity (DID) and Blockchain: Decentralized identity (DID) systems, often built on blockchain, give individuals control over their digital credentials. Only minimal proof is shared when verification is needed, such as confirming age without revealing personal details. Use cases include travel verification, secure healthcare record sharing, and simplified financial KYC. DIDs reduce reliance on large, breach-prone databases, empower users with control over their data, and enhance security and trust in digital interactions.
Benefits of Next-Generation Privacy Tech
Stronger Security: Next-generation privacy technologies protect sensitive information from breaches, hacks, and unauthorized access by minimizing data exposure and employing advanced cryptographic methods. These tools not only safeguard personal and corporate data but also reduce the risk of costly disruptions and reputational damage. Organizations can monitor and respond to potential threats more effectively, creating a resilient security framework that adapts to evolving cyber risks.
Regulatory Compliance: Advanced privacy technologies help organizations meet global standards such as GDPR, CCPA, and DPDP, avoiding hefty fines and legal repercussions. By integrating privacy-by-design principles, companies can ensure that data collection, storage, and processing adhere to regulatory requirements. This proactive approach also simplifies audits, reduces compliance overhead, and demonstrates accountability to regulators and stakeholders.
Enhanced User Trust: Customers are more likely to engage with companies that respect their privacy, creating long-term loyalty and brand advocacy. By demonstrating transparency in data practices and offering greater control over personal information, organizations can strengthen relationships with users. Trust built through strong privacy practices can also translate into higher conversion rates, repeat business, and positive word-of-mouth.
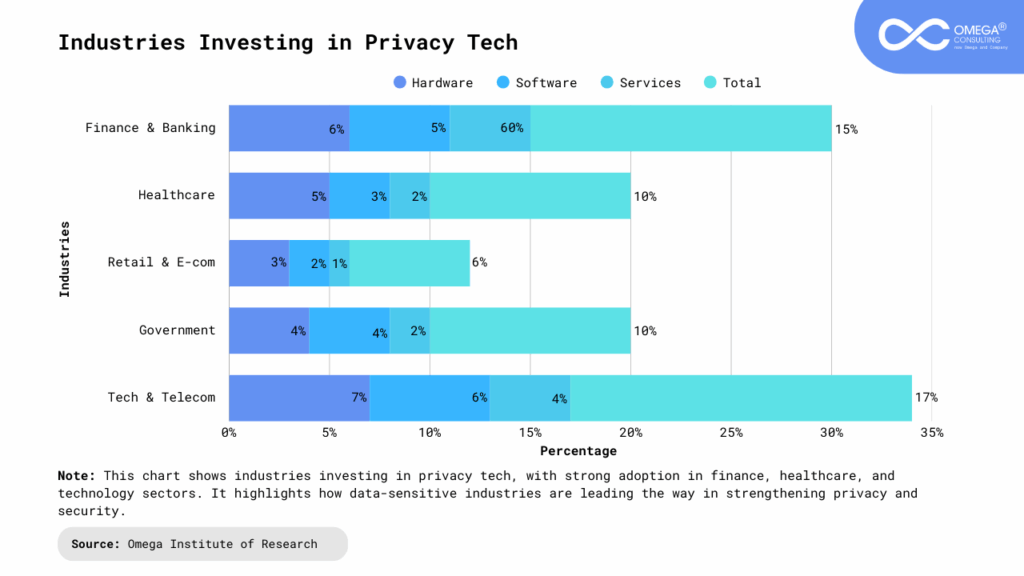
Encouraging Innovation: When privacy is assured, industries such as healthcare, finance, and AI can collaborate and innovate more freely without compromising sensitive data. Next-generation privacy tools enable secure sharing of insights, confidential research, and cross-organization AI model training. This fosters a culture of innovation while maintaining ethical standards, enabling companies to explore new technologies and business models with confidence.
Competitive Advantage: Businesses that invest early in privacy technology can stand out as trusted leaders in their industries, attracting privacy-conscious customers and partners. Demonstrating a commitment to robust data protection enhances brand reputation and differentiates a company in crowded markets. Over time, these organizations can leverage privacy as a strategic asset, turning compliance and security into a driver for growth, market trust, and customer loyalty.
Challenges to Overcome
Despite the promise, implementing next-gen privacy solutions is not without hurdles:
Cost & Complexity: Implementing advanced encryption, zero-knowledge proofs, and blockchain-based systems can be expensive and resource-intensive, requiring specialized expertise and infrastructure. Small and medium-sized businesses may find initial investments particularly challenging, while large organizations must navigate integration with existing systems. Additionally, ongoing maintenance, updates, and staff training contribute to both financial and operational complexity, making careful planning essential for successful deployment.
Scalability: Technologies like homomorphic encryption and federated learning are still computationally intensive, which can limit their effectiveness at enterprise scale. Processing large volumes of data or high-frequency transactions may require significant computing power and optimization. Organizations must carefully evaluate performance trade-offs, invest in high-performance infrastructure, and develop strategies for scaling privacy solutions without compromising efficiency or responsiveness.
User Experience: Privacy tools must strike a balance between robust security and seamless usability. Overly complex interfaces or cumbersome verification steps can frustrate users and discourage adoption, undermining the benefits of the technology. Designing intuitive workflows, clear consent mechanisms, and transparent privacy features is critical to ensure users feel secure without sacrificing convenience or engagement.
Interoperability: Different platforms, industries, and regions often adopt varying standards for privacy, data handling, and encryption, complicating global implementation. Organizations operating across borders may face conflicting regulations and technical incompatibilities. Achieving seamless interoperability requires alignment of protocols, collaboration with partners, and adherence to both regional laws and international best practices to ensure consistent and reliable privacy protection.
The Future of Privacy in a Hyperconnected World
As digital ecosystems expand with 5G, IoT, edge computing, and AI, data will become increasingly valuable and simultaneously more vulnerable making privacy a central concern for businesses and individuals alike. The future is likely to prioritize privacy-first innovation, where protecting data is not just a regulatory requirement but a core component of business strategy and competitive differentiation. Companies that adopt technologies such as Zero-Knowledge Proofs, homomorphic encryption, federated learning, differential privacy, and decentralized identity will benefit from stronger security, enhanced customer trust, and greater resilience against cyber threats. Over time, privacy will evolve from a defensive necessity into a strategic advantage, enabling organizations to innovate confidently, build lasting customer relationships, and maintain a competitive edge in an increasingly interconnected world.
Conclusion
The rise of hyperconnectivity has transformed how people live, work, and interact, but it has also amplified the risks surrounding data privacy. As cyber threats become more sophisticated and regulations increasingly strict, traditional security methods are no longer sufficient. Next-generation privacy technologies, including zero-knowledge proofs, homomorphic encryption, federated learning, differential privacy, and decentralized identity, offer a powerful evolution in safeguarding sensitive information. These innovations not only protect personal and organizational data but also foster trust, regulatory compliance, and innovation across industries such as healthcare, finance, e-commerce, and government services. While challenges like cost, scalability, and interoperability remain, the benefits far outweigh the hurdles, making investment in these technologies essential. Ultimately, the future of digital ecosystems will be shaped by organizations that adopt a privacy-first mindset, ensuring they can protect data, strengthen resilience, and build lasting trust with users in an increasingly hyperconnected world.
- https://moqod.com/blog/data-privacy-challenges-2025
- https://www.frost.com/growth-opportunity-news/the-future-of-privacy-in-a-hyper-connected-world/
- https://www.tamoco.com/blog/data-privacy-in-a-hyperconnected-world-how-people-and-businesses-are-taking-control/
- https://adengage.digital/future-of-privacy-in-a-hyper-connected-world/
Subscribe
Select topics and stay current with our latest insights
- Functions